
New data proves that while image generators drive massive download spikes, they fail the ultimate test of business viability: revenue conversion.

Cerebras is racing toward an IPO with a valuation that defies hardware gravity. But look closer at their revenue concentration and the OpenAI connection.

Dead as Disco transforme nos bibliothèques musicales en chorégraphies martiales, explorant le lien intime entre mélodie et réflexes.

Parents are clinging to 'safe' analog careers like aviation as AI threatens white-collar stability, but their logic is dangerously flawed.

Occitanie is rolling out the red carpet for Indian filmmakers, but building a sustainable media hub requires more than just sunshine and tax credits.

Photographer Grégoire Eloy isn't just taking photos; he's building a visual ledger of depreciating natural assets that markets can no longer ignore.

A deep explore Kratos, the PhaaS toolkit lowering the barrier for sophisticated cyberattacks targeting global enterprise infrastructure.

Intelligence reports reveal a surge in data breaches led by minors, highlighting a shift toward youth-driven cybercrime syndicates.

New data suggests the stereotypical elite hacker is a fantasy. The reality is younger, lonelier, and far more interested in social status than complex code.

The French government's long-delayed digital shield aims to block malicious websites in real-time, targeting phishing and online fraud attempts.
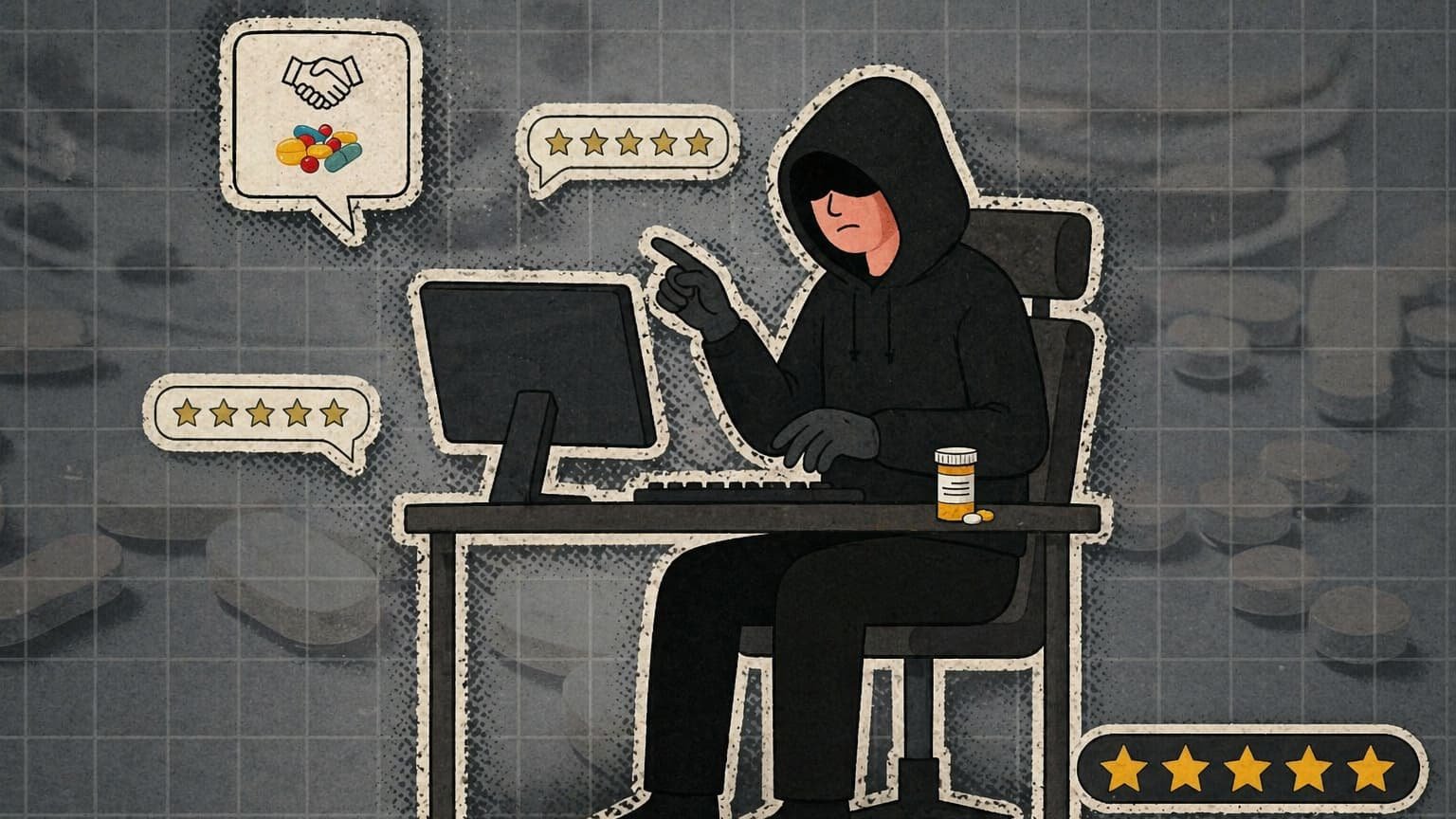
Drug traffickers are ditching the street corner for CRM systems and customer reviews. It's not a trend; it's a structural shift in how illegal goods move.

Surfshark One is moving beyond the VPN to build an all-in-one security platform. Here is why the bundle is the ultimate weapon against churn and legacy incumbents.