The Iranian Digital Front: Why State-Sponsored Hacking is the New Kinetic Reality
The Myth of the Purely Kinetic Conflict
The tech industry likes to pretend its creations exist in a vacuum of utility and progress, but the escalating friction in Iran proves otherwise. Software is no longer just the engine of commerce; it is the primary theater of modern engagement. Rahul Sasi and the team at CloudSEK are pointing to a shift that many observers have failed to grasp: the distinction between digital disruption and physical impact has effectively vanished.
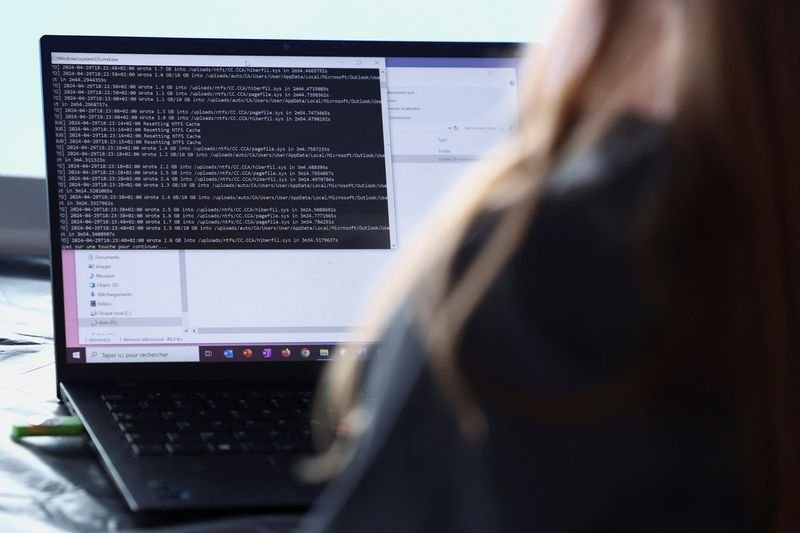
For years, we viewed state-sponsored hacking as a nuisance—a collection of defaced websites or stolen databases. That era ended when critical infrastructure became the target. In the current Iranian context, cyber operations are not merely supporting roles for traditional forces; they are the opening volleys designed to cripple a nation's ability to respond before a single boots-on-the-ground maneuver occurs.
The war in Iran has demonstrated how crucial cyberattacks have become in modern warfare, as these operations are now integral to military strategy.
This observation from CloudSEK highlights a grim reality for founders and developers alike. If your platform provides essential services, you are no longer a bystander in global politics. You are a potential logistical target. The security of a database is no longer just about protecting user privacy; it is about maintaining the stability of the social fabric during times of high-tension geopolitical maneuvering.
The Asymmetry of Digital Aggression
The beauty—and the terror—of this new age is its inherent asymmetry. A localized group of motivated developers can exert more pressure on a sovereign state than a mid-sized navy can. We are seeing a decentralization of power where private entities and independent actors influence the outcome of national conflicts. The barrier to entry for digital sabotage is exceptionally low compared to traditional hardware, yet the resulting chaos is disproportionately high.
Governments are scrambling to catch up, but their bureaucratic structures are ill-suited for the speed of a zero-day exploit. While a military might wait weeks for authorization, a state-sponsored hacker can pivot in minutes. This speed allows for a constant state of attrition that exhausts the defender’s resources and morale without ever declaring a formal state of hostilities.
Marketers and digital strategists often talk about 'engagement' as a metric for success. in cyber warfare, engagement means persistent presence within an adversary's network. It is about the long game of stealthy infiltration. The most effective attacks are the ones that remain undetected for months, quietly mapping out vulnerabilities until the moment of maximum political use arrives.
Infrastructure as the Ultimate Vulnerability
We have built our society on a stack of interconnected dependencies that were never designed to be defended against a nation-state. From power grids to financial clearinghouses, the underlying protocols are dangerously fragile. The Iranian conflict serves as a live-fire exercise for what happens when these systems are systematically tested by professional aggressors.
CloudSEK’s findings suggest that the focus has moved from simple data theft to operational disruption. It is one thing to lose credit card numbers; it is another entirely to lose control of the water supply or the electrical grid. This shift necessitates a complete rethink of how we build and deploy software at scale. Security can no longer be a feature added in the final sprint; it must be the core architecture upon which the entire product stands.
These cyber operations are not just about stealing secrets; they are about exercising power and control over an adversary's essential systems.
The quote underscores the psychological component of this trend. When a population loses trust in its basic infrastructure, the government’s legitimacy erodes. This is the ultimate goal of modern digital aggression: to win the conflict by breaking the will of the people through technological failure. It is a cleaner, quieter, and more efficient method of destabilization than anything we saw in the twentieth century.
If you are a startup founder today, ignore the geopolitical implications of your tech at your own peril. We are moving toward a period where every major software update is a potential vulnerability in the national defense. The conflict in Iran is not an isolated event; it is the blueprint for how power will be contested for the foreseeable future, and those who fail to fortify their systems will find themselves used as pawns in a match they didn't even know they were playing.
AI Film Maker — Script, voice & music by AI






























