The Passphrase Doctrine: Why Your Password Policy Is a Security Risk
The Complexity Paradox
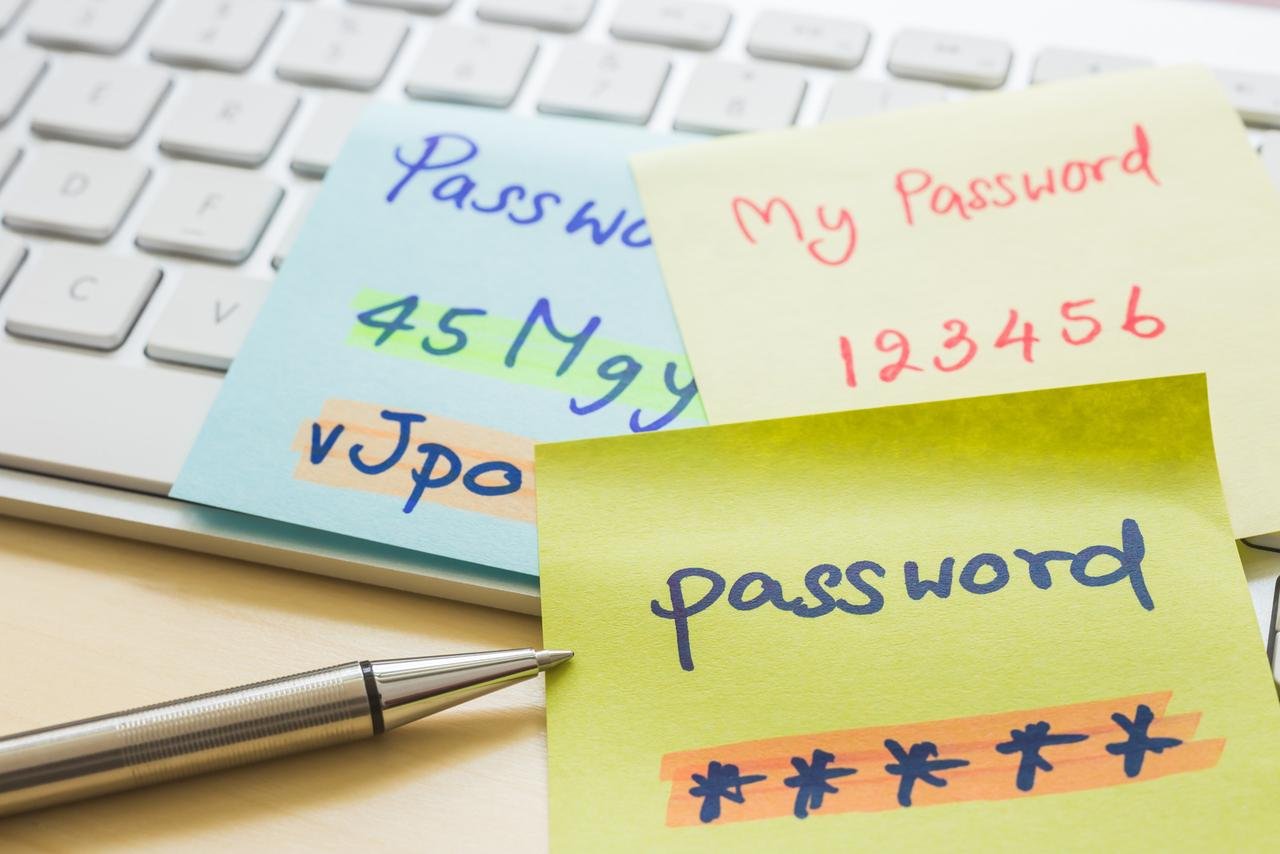
Security experts have spent two decades training users to behave like broken random number generators. We demanded eight characters, a capital letter, a digit, and a symbol, resulting in a global epidemic of P@ssword123!. The irony is that these 'complex' strings are trivial for modern hardware to brute-force, yet they are nearly impossible for a human brain to recall without writing them on a sticky note.
The industry is finally waking up to the fact that length beats complexity every single time. A password like Tr0ub4dor&3 is significantly weaker than a string of four random words like correct horse battery staple. While the former can be cracked in minutes by a specialized rig, the latter offers an exponential increase in entropy that would take centuries to decipher.
The length of a password is the primary factor in its resistance to brute-force attacks.
This observation by security researchers highlights the fundamental flaw in traditional IT policies. By forcing frequent resets and arbitrary character requirements, organizations actually encourage employees to use predictable patterns. A passphrase removes the friction between security and usability, creating a defense that actually works in the real world.
Entropy Over Obscurity
Building a passphrase isn't about being poetic; it is about maximizing mathematical uncertainty. When you pick four or five unrelated words, you are creating a search space so vast that standard dictionary attacks become useless. The trick is to ensure the words have no logical connection to your life or to each other.
Developers and founders often fall into the trap of using 'secure' strings that are actually just common substitutions. Replacing an 's' with a '$' or an 'a' with an '@' does nothing to stop modern cracking tools, which have these permutations baked into their algorithms from day one. True security comes from the sheer number of possible combinations that a 20-plus character string provides.
Users who are forced to use complex passwords will inevitably find ways to bypass the security measures, such as reuse or physical notes.
We see this behavior in every high-growth startup where speed is prioritized over protocol. If you make the security barrier too high to jump, people will simply walk around it. Passphrases offer a rare middle ground: they are computationally expensive to crack but mentally cheap to store. It is the only authentication method that respects the way the human brain actually functions.
Implementing the Human-Centric Standard
If you are still enforcing 90-day password rotations and special character requirements, you are living in 2005. Modern NIST guidelines have pivoted away from these practices because they create a false sense of security while frustrating the workforce. The shift toward passphrases is not just a trend; it is a necessary evolution in digital hygiene.
To create a truly unhackable string, you should aim for a minimum of fifteen characters. Do not overthink the selection process; the more random the sequence, the better the protection.
- Pick four common but unrelated nouns.
- Avoid famous quotes or song lyrics.
- Keep the spaces or use simple hyphens for readability.
The era of the 'unforgettable' complex password was a failure of imagination. We tried to make humans act like computers, and we failed. By adopting passphrases, we are finally allowing the math to do the heavy lifting while giving our memory a much-needed break. The strongest lock in the world is useless if you constantly lose the key; the passphrase ensures the key is always where you left it.
AI Video Creator — Veo 3, Sora, Kling, Runway































